Top suggestions for flow |
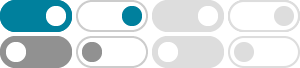
- Image size
- Color
- Type
- Layout
- People
- Date
- License
- Clear filters
- SafeSearch:
- Moderate
- Cyber Ethics
Flow Chart - Cyber Security Flow Chart
For Learning - Cyber Threats
Flow Chart - Cyber
Attack Action Flow Chart - Cyber Incident
Flow Chart - Cyber Crime
Flow Chart - Cyber Security Flow Chart
Poster - Cyber Security Incident Response
Flow Chart - Cyber Security
Flow Chart - Cyber
Incident Response Flow Chart - Cyber
Crime Flowchart - Cyber Bullying
Flow Chart - Cybersecurity Incident Response
Flow Chart - Flow Chart
Of Cyber Security - Flow Chart
Of Credit Card Fraud Detection - Credit Card Fraud Detection
Flow Chart - Hr Data Breach
Flow Chart - Data Breach Response
Flow Chart - Flow Chart
On Cyber Security - Types Of
Cyber Security Flow Chart
Some results have been hidden because they may be inaccessible to you.Show inaccessible results

 Feedback
Feedback